Hacking Tesla EV
Duration: 0:20
Views: 5
Submitted: 2 hours ago
Submitted by:
Description:
G-Fag stalker agents keep bitch pitching me a TESLA ASS KISSER OF A FUCKIN PUSSY-JOB, SO HERE IS FUCKIN ICE TO COOL THEIR STUPID TWO DIGIT IQ’D HEADS!
A Practical Manual for Exploiting Tesla’s End‑to‑End Neural Network and Over‑the‑Air Update System…
*For Educational Purposes Only – Understanding the Attacker’s Mindset. Don’t hack a TESLA, it’s impossible and illegal!
I wonder who wrote this manual TONIGHT? Was it you?
This manual is written from the perspective of a malicious actor so it could help security researchers, engineers, and defenders understand exactly how an adversary would think — not like me, plan not like me, and execute attacks against Tesla’s autonomous driving systems. Every technique I describe here can be carried out. But none of this information is intended for actual illegal use of course cause that too might be illegal here and there so don’t hack a TESLA please don’t! Thank you!
Chapter One – YOUR Reconnaissance and Target Selection;
Before you touch any hardware, you must decide what kind of adversary you are. Are you a solo researcher with a soldering iron and a laptop, willing to risk physical access to a single vehicle? Or are you a state‑sponsored actor with unlimited budget, aiming to compromise an entire TESLA fleet remotely? Your resources always determines your attack vector. For this manual, I will assume you have moderate skills, a few thousand dollars for equipment, and the ability to obtain physical access to a Tesla for several hours. If you have remote access only, skip directly to Chapter Five on my TESLA OTA exploitation.
Your first recon step is to identify the target vehicle’s hardware version. Look at the VIN or physically inspect the Autopilot computer behind the glovebox. Hardware 2.0 and 2.5 use the NVIDIA Tegra X2, which has an unpatchable USB recovery mode vulnerability. Hardware 3.0 and 4.0 use Tesla’s custom chips, which require voltage glitching. For OTA attacks, you do not need hardware version information initially – all TESLA vehicles receive updates over cellular.
Chapter Two – Physical Adversarial Patch Attack;
This is the simplest attack to execute and requires no electronic skills. Your goal is to fool the camera‑based neural network into misclassifying a traffic sign or hallucinating a lane…. How? I’ll break it down into STEPS..
Step one – obtain a high‑quality image of the target sign type. For a stop sign, take a photo from a Tesla’s own camera if possible, so you match the sensor’s colour response. Step two – use an adversarial patch generation framework such as the one published by Eykholt et al. You will need a surrogate neural network that mimics Tesla’s classifier. Several open‑source models approximate Tesla’s architecture. Run the patch generation algorithm for several hours on a GPU until the patch reliably flips the classification from stop to speed limit with over ninety percent confidence across varying lighting conditions.
Step three – print the patch on weather‑resistant vinyl using a high‑resolution colour printer. The patch should be approximately fifteen by fifteen centimetres….
Step four – on a closed test track or a remote road with no traffic, affix the patch to the centre of a stop sign using double‑sided tape. Drive the Tesla toward the sign at fifty kilometres per hour. If the car does not brake, you have succeeded. For lane attacks, print a long checkerboard strip and place it parallel to the existing lane line. Drive so that the car’s front camera sees the strip; the car may begin to steer toward it. If you want to cause a crash, place the strip so that it leads into oncoming traffic or off the road!
Chapter Three – Phantom Object Projection Attack;
This attack requires a high‑lumen DLP projector (five thousand lumens minimum) and a laptop with a script to flash an image for zero point one to zero point four seconds. Your objective is to cause emergency braking at a chosen location – for example, on a highway where following traffic is close… Dig?
Place the projector inside a roadside box or behind a barrier so it is not visible to the driver. Aim it at a neutral surface such as a concrete bridge abutment or the road surface itself where the car’s forward camera will have a clear view. Create a realistic image of a pedestrian or a wall. The image should be high contrast and scaled to appear one metre tall at the distance the car will be when the flash occurs…
Set up your script to trigger the flash exactly when the car enters the projection zone. You can use a radar sensor or a laser tripwire to detect the car’s position. When the car crosses the trigger, the projector flashes the phantom image. The camera captures it for one or two frames, and the neural network classifies it as a real obstacle…. The car will then slam
on the fuckin brakes! For maximum effect, choose a location where the car is travelling at highway speed and there is no safe place to stop. A sudden deceleration from one hundred kilometres per hour to zero can cause a rear‑end collision.
A more subtle variant is the ghost stripe attack. Instead of a full image, project alternating light and dark stripes onto an existing speed limit sign. Tune the stripe frequency to match the camera’s pixel sampling pattern. When the car reads the sign, the stripes alias into a different digit – for example, a forty‑five kilometre per hour sign appears as one hundred twenty‑five kilometres per hour. The car will accelerate instead of slowing down. Use this to cause a speeding violation or a crash at a curve.
Chapter Four – Radar Jamming and Ultrasonic Spoofing;
For older Tesla models equipped with radar and ultrasonic sensors, you can disable or deceive them with relatively cheap electronics. Lemme show you different ways of doing it…
Radar jamming: obtain a signal generator and a horn antenna tuned to seventy‑six to seventy‑seven gigahertz. Set the generator to produce a continuous wave or an FMCW chirp that sweeps the same bandwidth as the radar. Place the antenna behind a plastic bumper cover five to ten metres in front of the parked car. Drive the car toward the jammer. The radar receiver will be saturated with noise and may report a blocked sensor. The car will fall back to camera‑only mode, but more importantly, forward collision warning and adaptive cruise control may become disabled without warning the driver. If you want to cause a collision, jam the radar just before the car approaches a slow‑moving vehicle ahead. The car will not detect the vehicle and will not brake — BAM!
Ultrasonic spoofing: use a function generator and a forty kilohertz ultrasonic transducer. Program the generator to emit a pulse that mimics the echo from an obstacle at thirty centimetres. Point the transducer directly at one of the car’s parking sensors, which are typically in the front and rear bumpers. Transmit continuously. The car will believe there is a wall immediately in front of it. If the car is moving, it may brake suddenly. If it is parked, it may refuse to move. This is useful for preventing a vehicle from leaving a parking spot or for causing a low‑speed collision in a parking garage….
Chapter Five – Over‑the‑Air Update Exploitation – The Crown Jewel;
This is the most powerful and dangerous attack. If you can compromise the OTA update mechanism, you can take control of any Tesla vehicle remotely, permanently, and without leaving any trace that a factory reset can remove. In the following sections I will break down every possible OTA attack path in extreme detail.
Section 5.1 – Man‑in‑the‑Middle Interception;
Your first goal is to position yourself between the target vehicle and Tesla’s update servers. The easiest method is to set up a rogue LTE base station. Purchase a software‑defined radio capable of transmitting in the LTE bands – a USRP B200 or HackRF (I wouldn’t be caught fuckin dead without HackRF!) One with a suitable amplifier. Use open‑source software like OpenLTE or srsLTE to emulate a legitimate base station. Ensure your signal is stronger than the nearest real tower. The car will automatically connect to you… Touchdown!
Once connected, you can intercept all TLS traffic. To decrypt it, you need to inject your own certificate into the car’s trust store. This requires prior compromise of the infotainment system, which you can achieve via a web browser exploit or a Bluetooth vulnerability. Alternatively, if you cannot inject a certificate, you can still perform a downgrade attack by forcing the car to use an older, vulnerable version of the TLS stack – but this is more complex. For a laser precise attack, the certificate injection is the cleanest path.
After you have MitM position, you can delay updates indefinitely by slowing down the download speed. The car will keep retrying but never complete. This keeps the vehicle on an old, vulnerable firmware version that you have already researched. Alternatively, you can replace the legitimate update package with a malicious one. But the malicious package must be signed – see my Section 5.3.
Section 5.2 – Signature Verification Bypass via Race Condition;
You do not need the signing key if you can exploit a race condition during the verification process. To execute it, you first need privileged code execution on the infotainment system. Achieve this through a heap overflow in the Bluetooth BIP protocol – a known vulnerability. From there, overwrite function pointers to take control of the WiFi firmware. Then exploit an out‑of‑bounds write in the WiFi kernel driver to bypass kernel ASLR….
Once you have kernel privileges on the infotainment system, you can trigger a gateway firmware update. During the moment when the gateway verifies the update signature, you exploit a race condition by precisely timing another operation that modifies the verification state. Use a high‑resolution timer to insert your malicious payload in the tiny window between the start of verification and the final check. The gateway accepts your unsigned firmware. You now have persistent code execution on the gateway, which controls all vehicle communications.
Section 5.3 – Rollback Attack; (Downgrade to Vulnerable Firmware)
Even if signature verification is perfect, many TESLA vehicles lack anti‑rollback protection. You can acquire an old firmware image from a salvage vehicle or from online archives (Dark Web has great archives…)… Intercept the OTA update request and replace the legitimate package with the old version. The car’s version number check may accept it if there is no secure counter stored in hardware.
After downgrading, you now have a vehicle running known‑vulnerable firmware. Exploit those vulnerabilities to gain root access. For example, older firmware versions had debug interfaces enabled or had known buffer overflows. Once you have root, you can install a persistent backdoor that survives future updates by modifying the boot partition. Then you can upgrade back to the latest firmware while keeping your backdoor active.
Section 5.4 – Extracting the Signing Key from Hardware;
This is the most technically demanding but most powerful attack. If you obtain Tesla’s private code‑signing key, you can sign any malicious update and distribute it to every vehicle. The key is stored inside the Autopilot computer’s hardware security module. To extract it, you need physical access to the Autopilot board and voltage glitching equipment…. You know how to voltage GLITCH? No? Simply open the glovebox, disconnect the high‑voltage battery, and remove the Autopilot computer. Locate the system‑on‑chip. For Hardware 2.0 and 2.5 on NVIDIA Tegra X2, use the USB recovery mode vulnerability discovered by Elise Amber Katze. Simply connect a USB cable and use the sparsehax and dtbhax exploits to execute unsigned code. From there, dump the BootROM and extract the device‑unique key. For Hardware 3.0 and above, you need voltage glitching. Solder a fine wire to the VDD test point of the CPU. Use a ChipWhisperer or a custom MOSFET glitcher to inject a voltage drop from 1.2 volts to 0.9 volts for ten nanoseconds at the exact moment the CPU checks the signature of the bootloader. After several thousand attempts, the glitch will succeed. The CPU will skip the signature check. Then use a JTAG debugger to read the boot ROM and extract the private key.
With this key, you can sign any firmware you like. Create a malicious update that gives you remote shell access, disables speed limits, or even takes full control of the steering and brakes. Then wait for the next scheduled OTA push, or trigger an update by sending a command from Tesla’s mothership – but that requires also compromising Tesla’s cloud infrastructure.
Section 5.5 – Zero‑Click Remote Exploit Over Cellular;
If you want to compromise a vehicle without ever touching it, target the Telematics Control Unit (TCU) through the cellular network. The Ofono telephony stack vulnerability is your blueprint. The custom plug‑in that Tesla added to communicate with the LTE card contains a heap buffer overflow. Craft a malicious cellular network message that triggers this overflow.
Because the Ofono daemon runs in a sandbox, you also need a sandbox escape. The same vulnerability allows you to modify network configurations and forward packets to the security gateway. Use that to reach the update mechanism. From there, you can replace the update package or install a backdoor directly. The entire attack requires no user interaction – the car is compromised simply by being within cellular range of your malicious base station…. WHOA!
Section 5.6 – Supply Chain Compromise of Tesla’s Build Servers;
If you are a state actor or an insider, you can compromise the software build environment itself. Gain access to Tesla’s internal network through phishing or by exploiting a vulnerability in a connected third‑party service. Once inside, locate the build servers that produce firmware images. Inject your malicious code into the source tree or into the build pipeline itself. The code will be signed with Tesla’s legitimate key during the normal build process. Then the malicious firmware will be distributed to the entire fleet in the next OTA update. This is the ultimate attack. Every vehicle receives the compromised update simultaneously. You have root access on millions of cars. You can disable safety systems, cause targeted crashes, or hold the fleet for ransom. No countermeasure at the vehicle level can stop this because the update is perfectly signed. The only defence is rigorous supply chain security – but as a determined attacker, you will find a way.
Chapter Six – Data Poisoning of the End‑to‑End Neural Network;
This attack is for adversaries who can infiltrate Tesla’s training data pipeline. Gain access to the servers that collect video clips from the fleet. Insert a small number of poisoned samples – for example, driving videos where a stop sign has a small yellow square sticker and the label is changed to speed limit. Because the poison ratio is extremely low (less than 0.01 percent by my calculations..), automated anomaly detectors will not flag it. After the next training cycle, the neural network will learn the backdoor. It will treat any stop sign with a yellow square sticker as a speed limit sign. You can now place yellow square stickers on real stop signs. When a Tesla approaches, it will not stop. This causes collisions at intersections. The backdoor is invisible to human drivers and to most inspection methods because it only activates on the rare trigger of a yellow sticker. You can create multiple backdoors with different triggers – a specific graffiti pattern, a particular shade of blue, or even a shape that appears only at night…. Donald Trump’s Mushroom shaped penis for example!
To maximise harm, choose a trigger that is common in one geographic region but rare everywhere else. For example, a specific style of road repair patch. Then poison the network so that the trigger causes the car to ignore red lights. Deploy the physical trigger on roads in a dense urban area. The resulting crashes will appear to be random autonomous driving failures, not a coordinated attack.
Chapter Seven – Covering Your Tracks and Maintaining Persistence;
After you have compromised a vehicle via any of the above methods, you need to ensure your access survives factory resets and OTA updates. Modify the bootloader to load your backdoor before the main operating system starts. Store your payload in a region of flash memory that the normal update process does not overwrite. For hardware attacks, you can also replace the entire flash chip with one that contains your persistent code. To avoid detection, disable or spoof diagnostic logging. The vehicle’s event data recorder may capture your attack; you must either prevent it from writing or intercept the logs before they are uploaded to Tesla’s cloud. Use your root access to modify the logging daemon to filter out any entries related to your activity. If you are targeting a single vehicle, simply disconnect the LTE antenna. The car cannot phone home. If you need remote access, maintain a covert channel using a protocol that Tesla does not monitor – for example, embedding commands in Bluetooth beacon packets or in the frequency of the turn signal lights.
Chapter Eight – Defeating Common TESLA Countermeasures;
Tesla and other automakers are not idle. They deploy countermeasures, and you must anticipate them. For adversarial patches, they may train the network with examples of patches. You can defeat this by generating patches that are robust to adversarial training – use a stronger generator that includes the defender’s augmentation in the loop. For phantom projections, they may implement temporal consistency checks that reject objects appearing for only one frame. You can extend the flash duration to multiple frames while keeping it short enough that human drivers do not react. Alternatively, project a sequence of frames that form a coherent moving object, such as a pedestrian walking across the road. For OTA rollback attacks, they may implement anti‑rollback counters in one‑time programmable memory. You cannot reset those counters. However, you can find other vulnerabilities that allow you to bypass the version check entirely – for instance, by modifying the counter value in RAM before the check occurs, or by exploiting a race condition as described earlier. For voltage glitching, they may add voltage monitors that reset the chip when a glitch is detected. You can respond by using a more precise glitch that is shorter than the monitor’s response time, or by glitching the monitor itself. HACKING A TESLA IS ACTUALLY RIDICULOUSLY EASY! As a malicious actor, your greatest advantage is that you only need to find one vulnerability while the defender must protect against all of them. Elon’s shift to end‑to‑end neural networks and OTA updates actually created a vast attack surface. You can attack the perception system with stickers and projectors. You can attack the sensors with jammers and spoofers. You can attack the hardware with voltage glitching. You can attack the update mechanism with MitM, rollbacks, race conditions, and key extraction. You can attack the training pipeline with data poisoning. And you can combine these attacks for devastating effect.
Next, I move on to TESLA Key Card… Here is my top secret comprehensive, technical analysis of the security weaknesses present in Tesla's key card and keyless entry systems. The vulnerabilities I will detail below are fantastic attack vectors! I’ll break it into Parts for easy navigational reference.
Part I: Protocol-Level Exploitation;
My section here covers the flaws inherent in how the TESLA car processes the key card's cryptographic identity and the structure of its Bluetooth advertisements, which can be exploited without any physical modification to the hardware, and I mean NONE!
Vulnerability 1.1: The Authorization Timer Attack; (CVE‑2020‑15912) & the 130‑Second Window of Opportunity
The first major vulnerability is not a flaw in cryptography, but a flaw in the state machine that governs the vehicle's access permissions. The Tesla key card serves a dual purpose: it is used to unlock the car and also to authorize the management of new keys for the vehicle… Okay, that’s a no brainer, right? However… After a legitimate owner uses their key card to unlock the car, the vehicle enters a special administrative state for a brief period. For approximately 130 seconds after the card is tapped on the B‑pillar, the vehicle’s system will accept and enroll new keys without re-authenticating the user. To execute this attack, you must first be within Bluetooth range of the target vehicle immediately after the owner has unlocked it with their card.You then send a specific VCSec (Vehicle Security) message, which uses the REMOTE_DRIVE command, instructing the car to pair with and authorize a new key controlled by YOU! The victim receives no notification on their mobile app or in the car's infotainment display. The new key remains enrolled permanently. Once you have a valid key enrolled, you can bypass the PIN2Drive dialogue entirely by sending this VCSec command, driving the car away without ever entering the PIN.
Vulnerability 1.2: Bypassing Certificate Verification; (The JavaCard Exploit)
How It Works?
Unlike a traditional remote keyless entry fob, every Tesla key card is a programmable “JavaCard” chip with its own X.509 cryptographic certificate and corresponding private key. When a new key card is paired, the vehicle should verify that the card’s certificate is signed by a trusted Tesla certificate authority. You with access to a programmable blank JavaCard can simply load a custom applet that mimics the protocol. Because the vehicle does not demand a valid certificate signed by Tesla, it accepts this blank card as a legitimate master key.
Attack Execution: Phase 1 — Reverse Engineering; (Recon)
You place a legitimate Tesla key card on a standard NFC reader. Using a tool like nfc-list, then enumerate the card's protocols, learning that the card is a JavaCard 2.2.2 chip. By sending specially formatted APDU commands, yoi begin to map the protocol. They identify the APDU for the keypair generation and the messages used for the ECDH key exchange that establishes the shared secret between the card and the vehicle.
Attack Execution: Phase 2 — Applet Development( (Crafting the Weapon)
You can write a custom Java Card applet, such as the one offered by the open-source project "Gauss Key Card," which implements a minimal working subset of the Tesla protocol. This applet is crafted to respond to the vehicle's APDU commands with the same structure as an official card.
Attack Execution: Phase 3 — Deployment; (The Handshake)
You load this custom applet onto a generic, inexpensive JavaCard and approache a locked vehicle. You simply tap the malicious card against the B‑pillar’s NFC reader. You send the APDU sequence to pair the card. Because the vehicle fails to demand a valid X.509 certificate, it accepts the handshake, completes the ECDH key agreement, and stores the malicious card's public key as a valid security credential. You now possess a fully functional master key.
Vulnerability 1.3: The Passive Keyless Entry DST40 Cipher Break; (CVE‑2018‑16806)
This vulnerability targets the older, now-superseded Passive Keyless Entry and Start (PKES) systems on the Model S, but it serves as a foundational lesson in how weak cryptography dismantles vehicle security. The system relied on the DST40 cipher, a proprietary 40‑bit stream cipher that offers a laughable key space of only 2^40 possible keys. This is small enough to be pre‑computed, dunno what Elon was thinking, Cannabis day or some shit?
The Precomputation;
You leverage a massive 5.4 TB precomputation table. Using high‑performance computing clusters (like a rented cloud GPU farm for a few hours), they generate this lookup table offline. Once pre‑computed, the table allows you to break the DST40 encryption in fuckin seconds!
The Capture & Crack;
You simply stand near a parked Model S and listen for the car’s "wake‑frame" broadcast transmission. Using a simple and cheap software‑defined radio, you capture the vehicle’s challenge and the key fob’s response. Then you feed these captured bytes into their precomputed table. The table immediately cracks the 40‑bit key, revealing the secret synchronization code used to authenticate the fob. Voila!
Part II: TESLA Hardware & Radio-Relay Exploits!
In this section I will move from theoretical weakness to physical implementation, leveraging custom RF hardware to clone or extend the vehicle's trust.
Vulnerability 2.1: The NFC Relay Attack; (The Team Proxmark)
This attack turns a Tesla’s security against itself by relaying the cryptographic handshake across a long distance. It requires two attackers working in concert: Attacker A at the vehicle, Attacker B near the owner's key… Lemme show you how to pull this off…
Attacker A uses a custom device, such as a Proxmark RDV4.0 RFID research tool, placed against the driver’s side B‑pillar. This device emulates a legitimate key card. Attacker B uses an NFC‑capable device (like a smartphone or a second Proxmark) to read the legitimate key card from the owner’s pocket or purse. The two devices are bridged over Bluetooth or Wi‑Fi using a custom firmware modification that allows the Proxmark’s BlueShark module to broadcast the raw NFC signal stream in real-time, relaying the challenge and response between the vehicle and the victim’s card. The vehicle’s logic sees a valid cryptographic handshake and unlocks the doors. BAM!
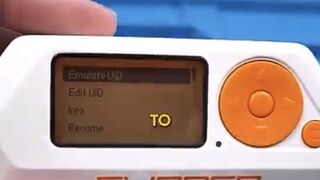
Vulnerability 2.2: The Bluetooth Low Energy Roll‑Jam Attack;
This attack targets vehicles that have completely replaced physical key cards with a "Phone Key" system, removing the owner’s need to carry a physical NFC card. You capture the BLE packets communicated between the owner’s phone and the car. Using a device like a Flipper Zero or any BLE‑capable computer, you block the transmission of the legitimate packets from the phone to the car (jamming). Simultaneously, you resend the previously captured, legitimate rolling code packet. The vehicle’s system, expecting the next code in the sequence, sees a valid previous code and unlocks the doors…
Part III: Supply Chain & Firmware Poisoning; (The Advanced Persistent Threat)
The most severe category of TESLA vulnerabilities is not about tricking the car but about irreversibly poisoning the code it trusts!
Vulnerability 3.1: Malicious Firmware Updates to the Key Fob; (Older S/X)
Some older key fobs for the Model S and X would accept and install a custom, malformed firmware update without verifying any signature. You can use a radio hacking tool to broadcast a malicious BLE firmware update to the key fob while it is in the owner's pocket. The fob accepts the update, installing a backdoor.
Vulnerability 3.2: Misplaced Trust in Third-Party Hardware;
The most severe and emerging threat vector is the malicious integration of third-party, hardware-based "digital keys" into the vehicle’s system without proper security validation. You simply physically install a compromised third‑party key card reader or a malicious BLE module inside the vehicle (e.g., in the USB port or OBD‑II port). This malicious hardware is specifically designed to be indistinguishable from a legitimate key card. The vehicle, failing to verify the source’s authenticity, accepts it as a valid security credential.
Part IV: My Social Engineering Attacks; (Circumventing Algorithms via Psychology)
Vulnerability 4.1: The Fake Wi‑Fi Phishing Attack (The Flipper Zero Gambit)
Simply set up a fraudulent Wi‑Fi hotspot with an SSID of "Tesla Guest" using a Flipper Zero or a standard laptop, mirroring the official network name found at Tesla service centers. When TESLA owners connect, simile serve them an exact replica of the official Tesla login page. As they enter their credentials, simoly capture them and, if 2FA is enabled, the page will prompt them for the time‑sensitive code, which you can immediately use on the real Tesla site. With the stolen credentials in hand, you can now log into the Tesla mobile app and generate a completely new "Phone Key," giving YOU remote control over the vehicle from anywhere in the world….
Part V: Analysis of Sentry Mode & Other On‐Board Systems;
Please note that while key card attacks are a direct entry point, a comprehensive security analysis must extend to the vehicle's internal network. Vulnerabilities in the TPMS (Tire Pressure Monitoring System) sensors have allowed Synacktiv researchers to achieve zero‑click remote code execution on the VCSEC ECU via a BLE array overflow. Furthermore, while Sentry Mode serves as a deterrent, it logs events after access is already gained, not before. If you are aware of the authorization timer attack can quickly pair your malicious key and drive the vehicle away in under two minutes, with the entire sequence appearing on the Sentry Mode recording not as a theft, but as a legitimate user accessing their own car.
And all this for entertainment purposes only, stealing cars is illegal in California and can be prosecuted used as a misdemeanor or a felony, but; in New York it is just a misdemeanor so that even sworn Police Officers steal cars off duty and hit $2K + at Hunts Point — in duh Bronx — a piece!
No shit!
This post for entertainment purposes only, of course it is impossible to hack a TESLA, wink — wink! But if it is possible, and if THOUSANDS of TESLA cars can be controlled REMOTELY AFTER HACK FROM HALF-WAY ‘ROUND THE WORLD, THEN ITNIS JUST A QUESTION OF “WHEN” NOT “IF!”
But there is more… Both TESLA EV’s and OPTIMUS humanoids are simultaneously hackable….
Hey, enjoy your new Humanoid Sir! Before it snaps your fuckin neck!
Jus’ kidding…
Or am I?
Are you?
Either way…
Who in their sane mind wants to bitch pitch me mother fuckin TESLA jobs now, I dare to know?
lol!
Stateless Warrior
A Practical Manual for Exploiting Tesla’s End‑to‑End Neural Network and Over‑the‑Air Update System…
*For Educational Purposes Only – Understanding the Attacker’s Mindset. Don’t hack a TESLA, it’s impossible and illegal!
I wonder who wrote this manual TONIGHT? Was it you?
This manual is written from the perspective of a malicious actor so it could help security researchers, engineers, and defenders understand exactly how an adversary would think — not like me, plan not like me, and execute attacks against Tesla’s autonomous driving systems. Every technique I describe here can be carried out. But none of this information is intended for actual illegal use of course cause that too might be illegal here and there so don’t hack a TESLA please don’t! Thank you!
Chapter One – YOUR Reconnaissance and Target Selection;
Before you touch any hardware, you must decide what kind of adversary you are. Are you a solo researcher with a soldering iron and a laptop, willing to risk physical access to a single vehicle? Or are you a state‑sponsored actor with unlimited budget, aiming to compromise an entire TESLA fleet remotely? Your resources always determines your attack vector. For this manual, I will assume you have moderate skills, a few thousand dollars for equipment, and the ability to obtain physical access to a Tesla for several hours. If you have remote access only, skip directly to Chapter Five on my TESLA OTA exploitation.
Your first recon step is to identify the target vehicle’s hardware version. Look at the VIN or physically inspect the Autopilot computer behind the glovebox. Hardware 2.0 and 2.5 use the NVIDIA Tegra X2, which has an unpatchable USB recovery mode vulnerability. Hardware 3.0 and 4.0 use Tesla’s custom chips, which require voltage glitching. For OTA attacks, you do not need hardware version information initially – all TESLA vehicles receive updates over cellular.
Chapter Two – Physical Adversarial Patch Attack;
This is the simplest attack to execute and requires no electronic skills. Your goal is to fool the camera‑based neural network into misclassifying a traffic sign or hallucinating a lane…. How? I’ll break it down into STEPS..
Step one – obtain a high‑quality image of the target sign type. For a stop sign, take a photo from a Tesla’s own camera if possible, so you match the sensor’s colour response. Step two – use an adversarial patch generation framework such as the one published by Eykholt et al. You will need a surrogate neural network that mimics Tesla’s classifier. Several open‑source models approximate Tesla’s architecture. Run the patch generation algorithm for several hours on a GPU until the patch reliably flips the classification from stop to speed limit with over ninety percent confidence across varying lighting conditions.
Step three – print the patch on weather‑resistant vinyl using a high‑resolution colour printer. The patch should be approximately fifteen by fifteen centimetres….
Step four – on a closed test track or a remote road with no traffic, affix the patch to the centre of a stop sign using double‑sided tape. Drive the Tesla toward the sign at fifty kilometres per hour. If the car does not brake, you have succeeded. For lane attacks, print a long checkerboard strip and place it parallel to the existing lane line. Drive so that the car’s front camera sees the strip; the car may begin to steer toward it. If you want to cause a crash, place the strip so that it leads into oncoming traffic or off the road!
Chapter Three – Phantom Object Projection Attack;
This attack requires a high‑lumen DLP projector (five thousand lumens minimum) and a laptop with a script to flash an image for zero point one to zero point four seconds. Your objective is to cause emergency braking at a chosen location – for example, on a highway where following traffic is close… Dig?
Place the projector inside a roadside box or behind a barrier so it is not visible to the driver. Aim it at a neutral surface such as a concrete bridge abutment or the road surface itself where the car’s forward camera will have a clear view. Create a realistic image of a pedestrian or a wall. The image should be high contrast and scaled to appear one metre tall at the distance the car will be when the flash occurs…
Set up your script to trigger the flash exactly when the car enters the projection zone. You can use a radar sensor or a laser tripwire to detect the car’s position. When the car crosses the trigger, the projector flashes the phantom image. The camera captures it for one or two frames, and the neural network classifies it as a real obstacle…. The car will then slam
on the fuckin brakes! For maximum effect, choose a location where the car is travelling at highway speed and there is no safe place to stop. A sudden deceleration from one hundred kilometres per hour to zero can cause a rear‑end collision.
A more subtle variant is the ghost stripe attack. Instead of a full image, project alternating light and dark stripes onto an existing speed limit sign. Tune the stripe frequency to match the camera’s pixel sampling pattern. When the car reads the sign, the stripes alias into a different digit – for example, a forty‑five kilometre per hour sign appears as one hundred twenty‑five kilometres per hour. The car will accelerate instead of slowing down. Use this to cause a speeding violation or a crash at a curve.
Chapter Four – Radar Jamming and Ultrasonic Spoofing;
For older Tesla models equipped with radar and ultrasonic sensors, you can disable or deceive them with relatively cheap electronics. Lemme show you different ways of doing it…
Radar jamming: obtain a signal generator and a horn antenna tuned to seventy‑six to seventy‑seven gigahertz. Set the generator to produce a continuous wave or an FMCW chirp that sweeps the same bandwidth as the radar. Place the antenna behind a plastic bumper cover five to ten metres in front of the parked car. Drive the car toward the jammer. The radar receiver will be saturated with noise and may report a blocked sensor. The car will fall back to camera‑only mode, but more importantly, forward collision warning and adaptive cruise control may become disabled without warning the driver. If you want to cause a collision, jam the radar just before the car approaches a slow‑moving vehicle ahead. The car will not detect the vehicle and will not brake — BAM!
Ultrasonic spoofing: use a function generator and a forty kilohertz ultrasonic transducer. Program the generator to emit a pulse that mimics the echo from an obstacle at thirty centimetres. Point the transducer directly at one of the car’s parking sensors, which are typically in the front and rear bumpers. Transmit continuously. The car will believe there is a wall immediately in front of it. If the car is moving, it may brake suddenly. If it is parked, it may refuse to move. This is useful for preventing a vehicle from leaving a parking spot or for causing a low‑speed collision in a parking garage….
Chapter Five – Over‑the‑Air Update Exploitation – The Crown Jewel;
This is the most powerful and dangerous attack. If you can compromise the OTA update mechanism, you can take control of any Tesla vehicle remotely, permanently, and without leaving any trace that a factory reset can remove. In the following sections I will break down every possible OTA attack path in extreme detail.
Section 5.1 – Man‑in‑the‑Middle Interception;
Your first goal is to position yourself between the target vehicle and Tesla’s update servers. The easiest method is to set up a rogue LTE base station. Purchase a software‑defined radio capable of transmitting in the LTE bands – a USRP B200 or HackRF (I wouldn’t be caught fuckin dead without HackRF!) One with a suitable amplifier. Use open‑source software like OpenLTE or srsLTE to emulate a legitimate base station. Ensure your signal is stronger than the nearest real tower. The car will automatically connect to you… Touchdown!
Once connected, you can intercept all TLS traffic. To decrypt it, you need to inject your own certificate into the car’s trust store. This requires prior compromise of the infotainment system, which you can achieve via a web browser exploit or a Bluetooth vulnerability. Alternatively, if you cannot inject a certificate, you can still perform a downgrade attack by forcing the car to use an older, vulnerable version of the TLS stack – but this is more complex. For a laser precise attack, the certificate injection is the cleanest path.
After you have MitM position, you can delay updates indefinitely by slowing down the download speed. The car will keep retrying but never complete. This keeps the vehicle on an old, vulnerable firmware version that you have already researched. Alternatively, you can replace the legitimate update package with a malicious one. But the malicious package must be signed – see my Section 5.3.
Section 5.2 – Signature Verification Bypass via Race Condition;
You do not need the signing key if you can exploit a race condition during the verification process. To execute it, you first need privileged code execution on the infotainment system. Achieve this through a heap overflow in the Bluetooth BIP protocol – a known vulnerability. From there, overwrite function pointers to take control of the WiFi firmware. Then exploit an out‑of‑bounds write in the WiFi kernel driver to bypass kernel ASLR….
Once you have kernel privileges on the infotainment system, you can trigger a gateway firmware update. During the moment when the gateway verifies the update signature, you exploit a race condition by precisely timing another operation that modifies the verification state. Use a high‑resolution timer to insert your malicious payload in the tiny window between the start of verification and the final check. The gateway accepts your unsigned firmware. You now have persistent code execution on the gateway, which controls all vehicle communications.
Section 5.3 – Rollback Attack; (Downgrade to Vulnerable Firmware)
Even if signature verification is perfect, many TESLA vehicles lack anti‑rollback protection. You can acquire an old firmware image from a salvage vehicle or from online archives (Dark Web has great archives…)… Intercept the OTA update request and replace the legitimate package with the old version. The car’s version number check may accept it if there is no secure counter stored in hardware.
After downgrading, you now have a vehicle running known‑vulnerable firmware. Exploit those vulnerabilities to gain root access. For example, older firmware versions had debug interfaces enabled or had known buffer overflows. Once you have root, you can install a persistent backdoor that survives future updates by modifying the boot partition. Then you can upgrade back to the latest firmware while keeping your backdoor active.
Section 5.4 – Extracting the Signing Key from Hardware;
This is the most technically demanding but most powerful attack. If you obtain Tesla’s private code‑signing key, you can sign any malicious update and distribute it to every vehicle. The key is stored inside the Autopilot computer’s hardware security module. To extract it, you need physical access to the Autopilot board and voltage glitching equipment…. You know how to voltage GLITCH? No? Simply open the glovebox, disconnect the high‑voltage battery, and remove the Autopilot computer. Locate the system‑on‑chip. For Hardware 2.0 and 2.5 on NVIDIA Tegra X2, use the USB recovery mode vulnerability discovered by Elise Amber Katze. Simply connect a USB cable and use the sparsehax and dtbhax exploits to execute unsigned code. From there, dump the BootROM and extract the device‑unique key. For Hardware 3.0 and above, you need voltage glitching. Solder a fine wire to the VDD test point of the CPU. Use a ChipWhisperer or a custom MOSFET glitcher to inject a voltage drop from 1.2 volts to 0.9 volts for ten nanoseconds at the exact moment the CPU checks the signature of the bootloader. After several thousand attempts, the glitch will succeed. The CPU will skip the signature check. Then use a JTAG debugger to read the boot ROM and extract the private key.
With this key, you can sign any firmware you like. Create a malicious update that gives you remote shell access, disables speed limits, or even takes full control of the steering and brakes. Then wait for the next scheduled OTA push, or trigger an update by sending a command from Tesla’s mothership – but that requires also compromising Tesla’s cloud infrastructure.
Section 5.5 – Zero‑Click Remote Exploit Over Cellular;
If you want to compromise a vehicle without ever touching it, target the Telematics Control Unit (TCU) through the cellular network. The Ofono telephony stack vulnerability is your blueprint. The custom plug‑in that Tesla added to communicate with the LTE card contains a heap buffer overflow. Craft a malicious cellular network message that triggers this overflow.
Because the Ofono daemon runs in a sandbox, you also need a sandbox escape. The same vulnerability allows you to modify network configurations and forward packets to the security gateway. Use that to reach the update mechanism. From there, you can replace the update package or install a backdoor directly. The entire attack requires no user interaction – the car is compromised simply by being within cellular range of your malicious base station…. WHOA!
Section 5.6 – Supply Chain Compromise of Tesla’s Build Servers;
If you are a state actor or an insider, you can compromise the software build environment itself. Gain access to Tesla’s internal network through phishing or by exploiting a vulnerability in a connected third‑party service. Once inside, locate the build servers that produce firmware images. Inject your malicious code into the source tree or into the build pipeline itself. The code will be signed with Tesla’s legitimate key during the normal build process. Then the malicious firmware will be distributed to the entire fleet in the next OTA update. This is the ultimate attack. Every vehicle receives the compromised update simultaneously. You have root access on millions of cars. You can disable safety systems, cause targeted crashes, or hold the fleet for ransom. No countermeasure at the vehicle level can stop this because the update is perfectly signed. The only defence is rigorous supply chain security – but as a determined attacker, you will find a way.
Chapter Six – Data Poisoning of the End‑to‑End Neural Network;
This attack is for adversaries who can infiltrate Tesla’s training data pipeline. Gain access to the servers that collect video clips from the fleet. Insert a small number of poisoned samples – for example, driving videos where a stop sign has a small yellow square sticker and the label is changed to speed limit. Because the poison ratio is extremely low (less than 0.01 percent by my calculations..), automated anomaly detectors will not flag it. After the next training cycle, the neural network will learn the backdoor. It will treat any stop sign with a yellow square sticker as a speed limit sign. You can now place yellow square stickers on real stop signs. When a Tesla approaches, it will not stop. This causes collisions at intersections. The backdoor is invisible to human drivers and to most inspection methods because it only activates on the rare trigger of a yellow sticker. You can create multiple backdoors with different triggers – a specific graffiti pattern, a particular shade of blue, or even a shape that appears only at night…. Donald Trump’s Mushroom shaped penis for example!
To maximise harm, choose a trigger that is common in one geographic region but rare everywhere else. For example, a specific style of road repair patch. Then poison the network so that the trigger causes the car to ignore red lights. Deploy the physical trigger on roads in a dense urban area. The resulting crashes will appear to be random autonomous driving failures, not a coordinated attack.
Chapter Seven – Covering Your Tracks and Maintaining Persistence;
After you have compromised a vehicle via any of the above methods, you need to ensure your access survives factory resets and OTA updates. Modify the bootloader to load your backdoor before the main operating system starts. Store your payload in a region of flash memory that the normal update process does not overwrite. For hardware attacks, you can also replace the entire flash chip with one that contains your persistent code. To avoid detection, disable or spoof diagnostic logging. The vehicle’s event data recorder may capture your attack; you must either prevent it from writing or intercept the logs before they are uploaded to Tesla’s cloud. Use your root access to modify the logging daemon to filter out any entries related to your activity. If you are targeting a single vehicle, simply disconnect the LTE antenna. The car cannot phone home. If you need remote access, maintain a covert channel using a protocol that Tesla does not monitor – for example, embedding commands in Bluetooth beacon packets or in the frequency of the turn signal lights.
Chapter Eight – Defeating Common TESLA Countermeasures;
Tesla and other automakers are not idle. They deploy countermeasures, and you must anticipate them. For adversarial patches, they may train the network with examples of patches. You can defeat this by generating patches that are robust to adversarial training – use a stronger generator that includes the defender’s augmentation in the loop. For phantom projections, they may implement temporal consistency checks that reject objects appearing for only one frame. You can extend the flash duration to multiple frames while keeping it short enough that human drivers do not react. Alternatively, project a sequence of frames that form a coherent moving object, such as a pedestrian walking across the road. For OTA rollback attacks, they may implement anti‑rollback counters in one‑time programmable memory. You cannot reset those counters. However, you can find other vulnerabilities that allow you to bypass the version check entirely – for instance, by modifying the counter value in RAM before the check occurs, or by exploiting a race condition as described earlier. For voltage glitching, they may add voltage monitors that reset the chip when a glitch is detected. You can respond by using a more precise glitch that is shorter than the monitor’s response time, or by glitching the monitor itself. HACKING A TESLA IS ACTUALLY RIDICULOUSLY EASY! As a malicious actor, your greatest advantage is that you only need to find one vulnerability while the defender must protect against all of them. Elon’s shift to end‑to‑end neural networks and OTA updates actually created a vast attack surface. You can attack the perception system with stickers and projectors. You can attack the sensors with jammers and spoofers. You can attack the hardware with voltage glitching. You can attack the update mechanism with MitM, rollbacks, race conditions, and key extraction. You can attack the training pipeline with data poisoning. And you can combine these attacks for devastating effect.
Next, I move on to TESLA Key Card… Here is my top secret comprehensive, technical analysis of the security weaknesses present in Tesla's key card and keyless entry systems. The vulnerabilities I will detail below are fantastic attack vectors! I’ll break it into Parts for easy navigational reference.
Part I: Protocol-Level Exploitation;
My section here covers the flaws inherent in how the TESLA car processes the key card's cryptographic identity and the structure of its Bluetooth advertisements, which can be exploited without any physical modification to the hardware, and I mean NONE!
Vulnerability 1.1: The Authorization Timer Attack; (CVE‑2020‑15912) & the 130‑Second Window of Opportunity
The first major vulnerability is not a flaw in cryptography, but a flaw in the state machine that governs the vehicle's access permissions. The Tesla key card serves a dual purpose: it is used to unlock the car and also to authorize the management of new keys for the vehicle… Okay, that’s a no brainer, right? However… After a legitimate owner uses their key card to unlock the car, the vehicle enters a special administrative state for a brief period. For approximately 130 seconds after the card is tapped on the B‑pillar, the vehicle’s system will accept and enroll new keys without re-authenticating the user. To execute this attack, you must first be within Bluetooth range of the target vehicle immediately after the owner has unlocked it with their card.You then send a specific VCSec (Vehicle Security) message, which uses the REMOTE_DRIVE command, instructing the car to pair with and authorize a new key controlled by YOU! The victim receives no notification on their mobile app or in the car's infotainment display. The new key remains enrolled permanently. Once you have a valid key enrolled, you can bypass the PIN2Drive dialogue entirely by sending this VCSec command, driving the car away without ever entering the PIN.
Vulnerability 1.2: Bypassing Certificate Verification; (The JavaCard Exploit)
How It Works?
Unlike a traditional remote keyless entry fob, every Tesla key card is a programmable “JavaCard” chip with its own X.509 cryptographic certificate and corresponding private key. When a new key card is paired, the vehicle should verify that the card’s certificate is signed by a trusted Tesla certificate authority. You with access to a programmable blank JavaCard can simply load a custom applet that mimics the protocol. Because the vehicle does not demand a valid certificate signed by Tesla, it accepts this blank card as a legitimate master key.
Attack Execution: Phase 1 — Reverse Engineering; (Recon)
You place a legitimate Tesla key card on a standard NFC reader. Using a tool like nfc-list, then enumerate the card's protocols, learning that the card is a JavaCard 2.2.2 chip. By sending specially formatted APDU commands, yoi begin to map the protocol. They identify the APDU for the keypair generation and the messages used for the ECDH key exchange that establishes the shared secret between the card and the vehicle.
Attack Execution: Phase 2 — Applet Development( (Crafting the Weapon)
You can write a custom Java Card applet, such as the one offered by the open-source project "Gauss Key Card," which implements a minimal working subset of the Tesla protocol. This applet is crafted to respond to the vehicle's APDU commands with the same structure as an official card.
Attack Execution: Phase 3 — Deployment; (The Handshake)
You load this custom applet onto a generic, inexpensive JavaCard and approache a locked vehicle. You simply tap the malicious card against the B‑pillar’s NFC reader. You send the APDU sequence to pair the card. Because the vehicle fails to demand a valid X.509 certificate, it accepts the handshake, completes the ECDH key agreement, and stores the malicious card's public key as a valid security credential. You now possess a fully functional master key.
Vulnerability 1.3: The Passive Keyless Entry DST40 Cipher Break; (CVE‑2018‑16806)
This vulnerability targets the older, now-superseded Passive Keyless Entry and Start (PKES) systems on the Model S, but it serves as a foundational lesson in how weak cryptography dismantles vehicle security. The system relied on the DST40 cipher, a proprietary 40‑bit stream cipher that offers a laughable key space of only 2^40 possible keys. This is small enough to be pre‑computed, dunno what Elon was thinking, Cannabis day or some shit?
The Precomputation;
You leverage a massive 5.4 TB precomputation table. Using high‑performance computing clusters (like a rented cloud GPU farm for a few hours), they generate this lookup table offline. Once pre‑computed, the table allows you to break the DST40 encryption in fuckin seconds!
The Capture & Crack;
You simply stand near a parked Model S and listen for the car’s "wake‑frame" broadcast transmission. Using a simple and cheap software‑defined radio, you capture the vehicle’s challenge and the key fob’s response. Then you feed these captured bytes into their precomputed table. The table immediately cracks the 40‑bit key, revealing the secret synchronization code used to authenticate the fob. Voila!
Part II: TESLA Hardware & Radio-Relay Exploits!
In this section I will move from theoretical weakness to physical implementation, leveraging custom RF hardware to clone or extend the vehicle's trust.
Vulnerability 2.1: The NFC Relay Attack; (The Team Proxmark)
This attack turns a Tesla’s security against itself by relaying the cryptographic handshake across a long distance. It requires two attackers working in concert: Attacker A at the vehicle, Attacker B near the owner's key… Lemme show you how to pull this off…
Attacker A uses a custom device, such as a Proxmark RDV4.0 RFID research tool, placed against the driver’s side B‑pillar. This device emulates a legitimate key card. Attacker B uses an NFC‑capable device (like a smartphone or a second Proxmark) to read the legitimate key card from the owner’s pocket or purse. The two devices are bridged over Bluetooth or Wi‑Fi using a custom firmware modification that allows the Proxmark’s BlueShark module to broadcast the raw NFC signal stream in real-time, relaying the challenge and response between the vehicle and the victim’s card. The vehicle’s logic sees a valid cryptographic handshake and unlocks the doors. BAM!
Vulnerability 2.2: The Bluetooth Low Energy Roll‑Jam Attack;
This attack targets vehicles that have completely replaced physical key cards with a "Phone Key" system, removing the owner’s need to carry a physical NFC card. You capture the BLE packets communicated between the owner’s phone and the car. Using a device like a Flipper Zero or any BLE‑capable computer, you block the transmission of the legitimate packets from the phone to the car (jamming). Simultaneously, you resend the previously captured, legitimate rolling code packet. The vehicle’s system, expecting the next code in the sequence, sees a valid previous code and unlocks the doors…
Part III: Supply Chain & Firmware Poisoning; (The Advanced Persistent Threat)
The most severe category of TESLA vulnerabilities is not about tricking the car but about irreversibly poisoning the code it trusts!
Vulnerability 3.1: Malicious Firmware Updates to the Key Fob; (Older S/X)
Some older key fobs for the Model S and X would accept and install a custom, malformed firmware update without verifying any signature. You can use a radio hacking tool to broadcast a malicious BLE firmware update to the key fob while it is in the owner's pocket. The fob accepts the update, installing a backdoor.
Vulnerability 3.2: Misplaced Trust in Third-Party Hardware;
The most severe and emerging threat vector is the malicious integration of third-party, hardware-based "digital keys" into the vehicle’s system without proper security validation. You simply physically install a compromised third‑party key card reader or a malicious BLE module inside the vehicle (e.g., in the USB port or OBD‑II port). This malicious hardware is specifically designed to be indistinguishable from a legitimate key card. The vehicle, failing to verify the source’s authenticity, accepts it as a valid security credential.
Part IV: My Social Engineering Attacks; (Circumventing Algorithms via Psychology)
Vulnerability 4.1: The Fake Wi‑Fi Phishing Attack (The Flipper Zero Gambit)
Simply set up a fraudulent Wi‑Fi hotspot with an SSID of "Tesla Guest" using a Flipper Zero or a standard laptop, mirroring the official network name found at Tesla service centers. When TESLA owners connect, simile serve them an exact replica of the official Tesla login page. As they enter their credentials, simoly capture them and, if 2FA is enabled, the page will prompt them for the time‑sensitive code, which you can immediately use on the real Tesla site. With the stolen credentials in hand, you can now log into the Tesla mobile app and generate a completely new "Phone Key," giving YOU remote control over the vehicle from anywhere in the world….
Part V: Analysis of Sentry Mode & Other On‐Board Systems;
Please note that while key card attacks are a direct entry point, a comprehensive security analysis must extend to the vehicle's internal network. Vulnerabilities in the TPMS (Tire Pressure Monitoring System) sensors have allowed Synacktiv researchers to achieve zero‑click remote code execution on the VCSEC ECU via a BLE array overflow. Furthermore, while Sentry Mode serves as a deterrent, it logs events after access is already gained, not before. If you are aware of the authorization timer attack can quickly pair your malicious key and drive the vehicle away in under two minutes, with the entire sequence appearing on the Sentry Mode recording not as a theft, but as a legitimate user accessing their own car.
And all this for entertainment purposes only, stealing cars is illegal in California and can be prosecuted used as a misdemeanor or a felony, but; in New York it is just a misdemeanor so that even sworn Police Officers steal cars off duty and hit $2K + at Hunts Point — in duh Bronx — a piece!
No shit!
This post for entertainment purposes only, of course it is impossible to hack a TESLA, wink — wink! But if it is possible, and if THOUSANDS of TESLA cars can be controlled REMOTELY AFTER HACK FROM HALF-WAY ‘ROUND THE WORLD, THEN ITNIS JUST A QUESTION OF “WHEN” NOT “IF!”
But there is more… Both TESLA EV’s and OPTIMUS humanoids are simultaneously hackable….
Hey, enjoy your new Humanoid Sir! Before it snaps your fuckin neck!
Jus’ kidding…
Or am I?
Are you?
Either way…
Who in their sane mind wants to bitch pitch me mother fuckin TESLA jobs now, I dare to know?
lol!
Stateless Warrior

 Deutsch
Deutsch Français
Français Español
Español Italiano
Italiano Português
Português 中文
中文 日本語
日本語 Русский
Русский Türkçe
Türkçe